
911 service as it existed until July 28, 2022.
911[.]re, the agent service that has sold since 2015 access to hundreds of thousands of Microsoft Windows Computer Daily, announced this week that it is shutting down in the wake of a data breach that devastated key components of its business operations. The sudden shutdown comes ten days after KrebsOnSecurity published an in-depth look at 911 and its connections to shady pay-per-install affiliate programs that secretly combined 911 proxy programs with other addresses, including “free” utilities and pirated software.
911[.]repeat he is It was one of the original “residential proxy” networks, which allowed someone to rent a residential IP address to use as a relay for their Internet communications, providing anonymity and the advantage of being seen as a residential user browsing the web.
Residential proxy services are often marketed to people seeking the ability to evade country-specific bans by movie streaming providers and major media outlets. But some – like 911 – build their networks in part by offering “free VPN” or “free proxy” services that are powered by software that turns a user’s computer into a traffic relay for other users. In this scenario, users already get a free VPN service, but they often do not realize that doing so will turn their computer into a proxy that allows others to use their Internet address to conduct online transactions.
From a website perspective, it appears that the residential proxy network user’s IP traffic originates from the rented residential IP address, and not from the proxy service client. These services can legitimately be used for several commercial purposes – such as price comparisons or sales information – but are widely misused to mask cybercrime activity because they can make it difficult to trace malicious traffic back to its original source.
As noted in Crips on Security story on July 19 on 911The Agent Service operated several pay-per-install systems that prompted affiliates to surreptitiously associate the Agent program with other programs, continually creating a steady stream of new Agents for the Service.
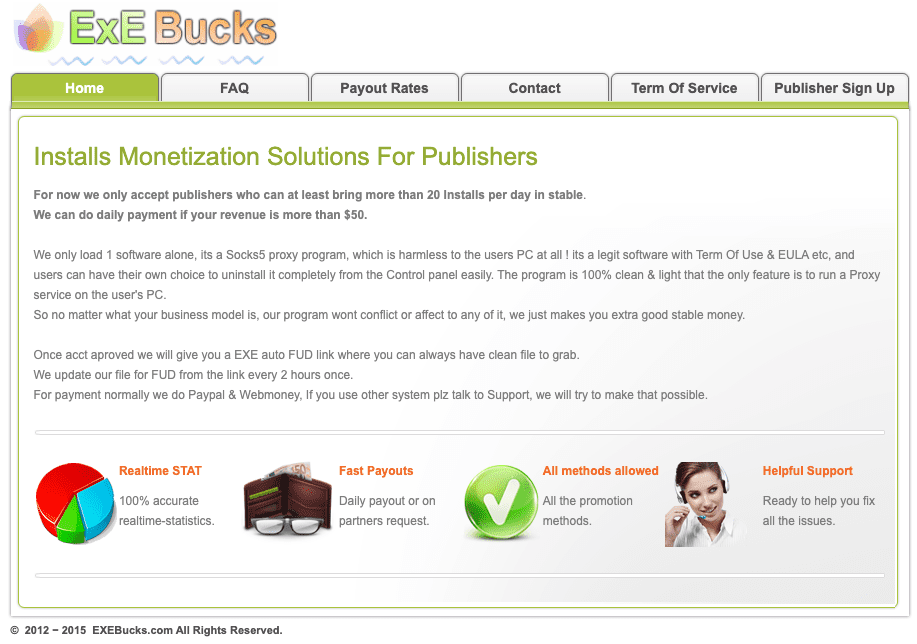
Cached flashupdate[.]net circa 2016, which shows that the homepage of a pay-to-install affiliate program spurred the silent installation of the 911 agent.
Within hours of that story, 911 posted a notice at the top of its site, saying: “We are reviewing our network and adding a series of security measures to prevent misuse of our services. Proxy top-up has closed and new user registration is closed. We review every existing user to ensure their use is legit and [in] Compliance with the Terms of Service.
In this announcement, all hell broke loose on several cybercrime forums, with many old 911 customers reporting that they were unable to use the service. Others affected by the outage said it appeared that 911 was trying to implement some kind of “know your customer” rule – perhaps 911 was just trying to weed out those customers who use the service for high volumes of cybercriminal activity.
Then on July 28, the 911 website began redirecting to a notice that said, “We regret to inform you that we have permanently closed 911 and all of its services on July 28.”
According to 911, the service was hacked in early July, and it was discovered that someone had tampered with the balances of a large number of user accounts. 911 said that the hackers misused an API that handles overloading accounts when users deposit money with the service.
The 911 message reads, “I’m not sure how the hacker got in.” “Therefore, we have urgently shut down the recharge system, registered a new user, and launched an investigation.”
911 said that although the hackers got in, they were also able to overwrite the critical 911[.]Restore servers, data, and backup copies of that data.
The statement continues: “On July 28, a large number of users reported that they were unable to log into the system.” “We found that the data on the server was maliciously damaged by the hacker, resulting in the loss of data and backups. It’s [sic] He confirmed that the recharging system was also hacked in the same way. We had to make this difficult decision due to the loss of important data that made the service unrecoverable.”
Operated largely outside of China, 911 has been a very popular service across many cybercrime forums, and has become something of a critical infrastructure for this community after two longtime 911 competitors – malware-based proxy services. VIP72 And the LuxSocks – They closed their doors last year.
Now, many crime forums who have relied on 911 for their operations are wondering aloud if there are any alternatives commensurate with the scale and usefulness offered by 911. The consensus seems to be a resounding “no.”
I think we may soon learn more about the security incidents that caused the 911 to explode. Perhaps other proxy services will emerge to meet what appears to be a growing demand for such services at the moment, with relatively little supply.
Meanwhile, the absence of 911 could coincide with a measurable (albeit only short-lived) delay in unwanted traffic to the Internet’s top destinations, including banks, retailers and cryptocurrency platforms, as many former agents of the proxy service scramble to make arrangements. alternative.
Riley KilmerCo-founder of the proxy tracking service SpirosThe 911 network will be difficult to replicate in the short term, he said.
“My guess [911’s remaining competitors] You’ll get a lot of support in the short term, but a new player will come in eventually,” Kilmer said. “None of these are good alternatives to LuxSocks or 911. However, all of them will allow anyone to use them. As for scam rates, attempts will continue but with these replacement services which should be easier to monitor and stop. 911 has some very clean IP addresses. “
911 wasn’t the only major proxy provider to disclose this week’s hack related to unauthenticated APIs: On July 28, KrebsOnSecurity reported that Exposed web internal APIs leaked from Microleaves’ customer database, which is a proxy service that rotates the IP addresses of its clients every five to ten minutes. This investigation showed that Microleaves, like the 911, had a long history of using pay-per-install schemes to spread its proxy software.

“Unapologetic communicator. Wannabe web lover. Friendly travel scholar. Problem solver. Amateur social mediaholic.”

